
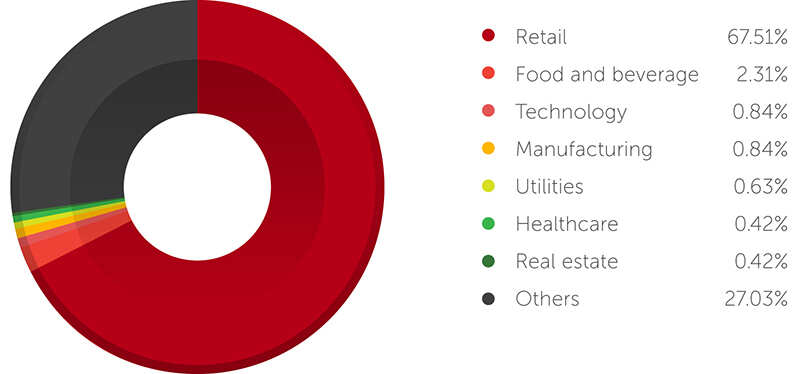
Categorization of POS RAM scrapping malware samples based on exfiltration | Download Scientific Diagram

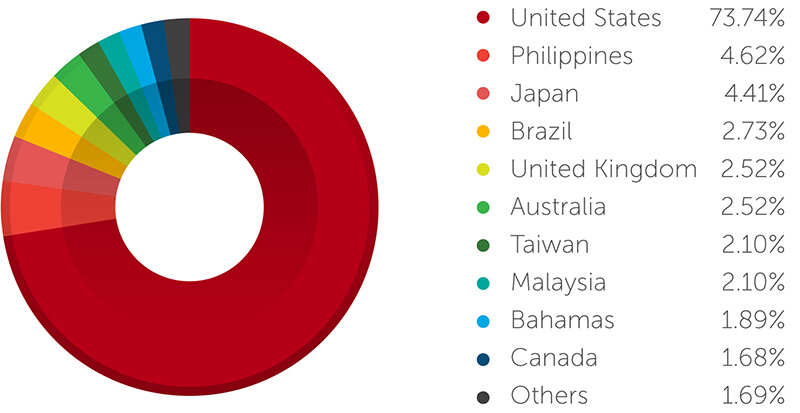
Categorization of POS RAM scrapping malware samples based on process... | Download Scientific Diagram

Stronger public key encryption system withstanding RAM scraper like attacks - Sivanandam - 2016 - Security and Communication Networks - Wiley Online Library









/cdn.vox-cdn.com/uploads/chorus_image/image/63705346/credit_card_swipe.0.1537497931.0.png)




