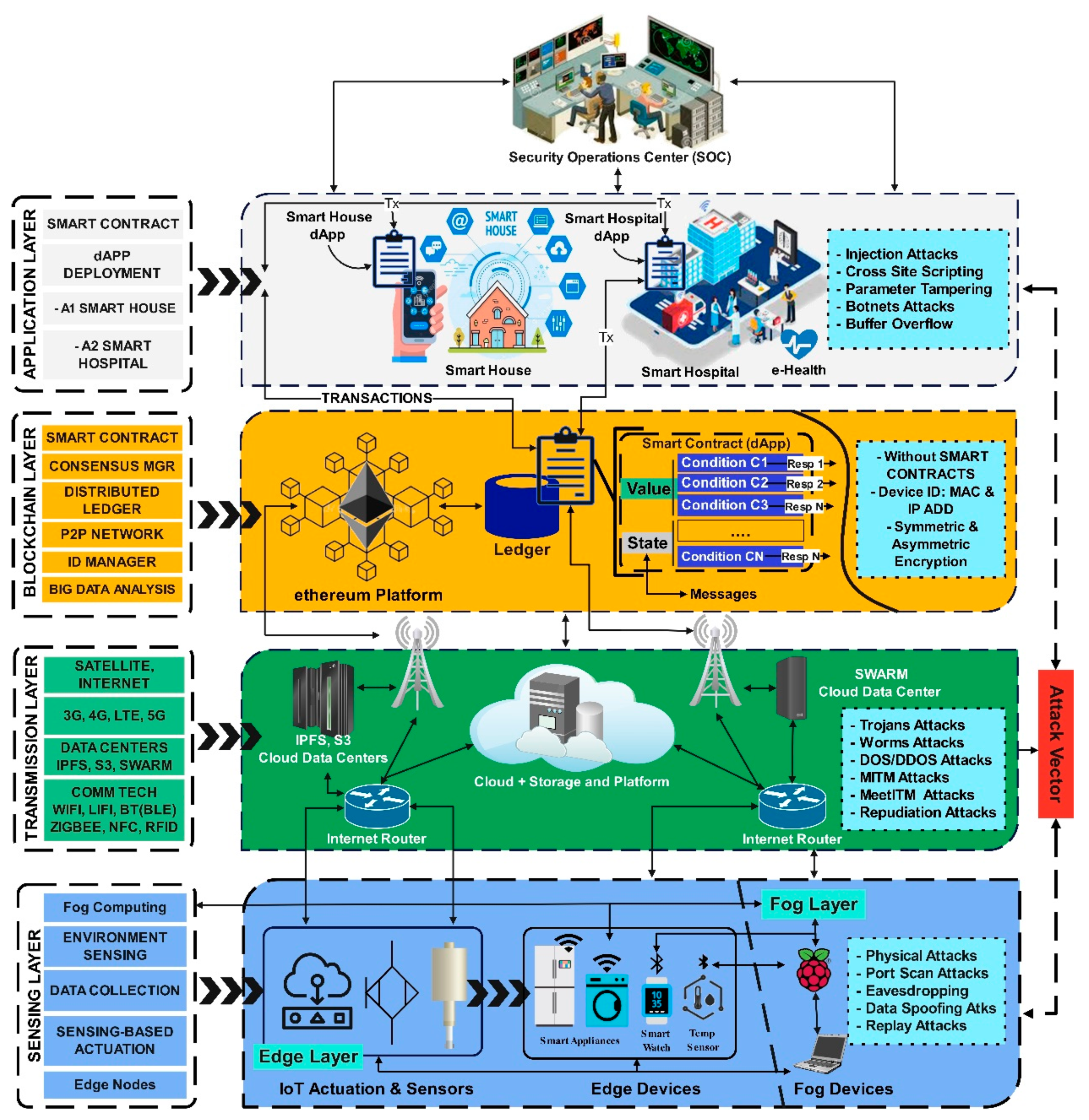
Sensors | Free Full-Text | A Comparative Analysis on Blockchain versus Centralized Authentication Architectures for IoT-Enabled Smart Devices in Smart Cities: A Comprehensive Review, Recent Advances, and Future Research Directions

A Blockchain‐based Cyber Attack Detection Scheme for Decentralized Internet of Things using Software‐Defined Network - Guha Roy - 2021 - Software: Practice and Experience - Wiley Online Library




![TUTO] Comment trouver l'ip de quelqu'un sur skype et le BOOT (DDOS) - YouTube TUTO] Comment trouver l'ip de quelqu'un sur skype et le BOOT (DDOS) - YouTube](https://i.ytimg.com/vi/iwYldG8VYsY/maxresdefault.jpg)